Get the report
MoreLog files are the primary data source for network observability. A log file is a computer-generated data file that contains information about usage patterns, activities, and operations within an operating system, application, server or another device. Log files show whether resources are performing properly and optimally.
Log files are automatically computer-generated whenever an event with a specific classification takes place on the network. The reason log files exist is that software and hardware developers find it easier to troubleshoot and debug their creations when they access a textual record of the events that the system is producing. Each of the leading operating systems is uniquely configured to generate and categorize event logs in response to specific types of events. Log management systems centralize all log files, to gather sort and analyze log data, and make it easy to understand, trace, and address key issues related to application performance.
Windows event logs
The windows operating system can generate an event log in response to activity on any of its hardware or software components. Network security and operations analysts can use specialized software tools to aggregate and analyze these logs, detect patterns and trends, and respond to incidents or potential user issues. Windows is pre-configured to classify events into six categories:
Linux event logs
The Linux operating system is uniquely configured to generate and store log files. Linux creates a continuous timeline of events that take place on the system, including every event related to the server, kernel, and running applications. Linux places events in four distinct categories:
These categories are analogous to those used by Windows O/S.
iOS event logs
iOS takes a unique approach to event log generation when compared to other operating systems. iOS does not log every event that happens in the system, but it does generate documentation for application crashes. Later versions of iOS (10.0 and beyond) offer an API that can be used to log application events that take place on the system. The iOS logging API allows network administrators to access log file data from:
Large IT organizations depend on an extensive network of IT infrastructure and applications to power key business services. Logfile monitoring and analysis increase the observability of this network, creating transparency and allowing visibility into the cloud computing environment. While observability should not be treated as an ultimate goal, it should always be seen as a mechanism for achieving real business objectives:
Log files include information about system performance that can be used to determine when additional capacity is needed to optimize the user experience. Log files can help analysts identify slow queries, errors that are causing transactions to take too long or bugs that impact website or application performance.
Log files capture things like unsuccessful log-in attempts, failed user authentication, or unexpected server overloads, all of which can signal to an analyst that a cyber attack might be in progress. The best security monitoring tools can send alerts and automate responses as soon as these events are detected on the network.
Log files capture the behavior of users within an application, giving rise to an area of inquiry known as user behavior analytics. By analyzing the actions of users within an application, developers can optimize the application to get users to their goals more quickly, improving customer satisfaction and driving revenue in the process.
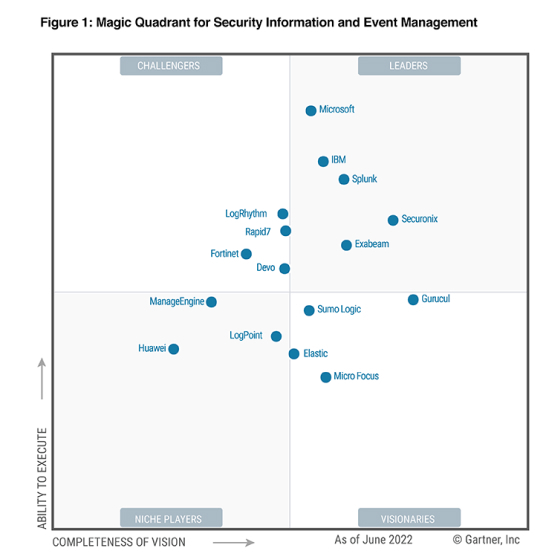
Sumo Logic is the industry-leading cloud-native platform that makes it easy for IT organizations to aggregate and analyze every log file generated within private, public or hybrid cloud environments. With Sumo Logic's log file analysis capabilities, your IT organization can identify new business risks and opportunities while responding efficiently to security threats and operational issues before they negatively impact users.
You can start monitoring and analyzing log files with Sumo Logic for free here.
Reduce downtime and move from reactive to proactive monitoring.